You might have heard the word “Bootloader” several times. Android devices with Qualcomm chipset have a PBL i.e. Primary Boot Loader. Understand it as the part of your chipset that boots up your device every time you turn ON your Android smartphone. However, few might know that there is an alternative boot mode as well which is called EDL mode. EDL (Emergency Download Mode) on Qualcomm chipsets allow the OEM to flash the software on the device in case of boot loop, or bricked devices. Keep in mind that this cannot be modified and has to take full control over the Android device’s storage.
Smartphone manufacturers like OnePlus, Xiaomi, etc have released a software tool which is called programmers that utilizes EDL and Firehouse protocol to unbrick the device. Firehouse can run a number of commands and also has the capability to examine the device’s data. And in this post, we will guide you on what is Qualcomm’s EDL mode and how do we access it. So, without any further ado, let us get straight into the article itself:
What is Qualcomm’s EDL mode? How do we access?
Before we head on to the details of the EDL mode, it is necessary to understand that according to security researchers Roee Hay (@roeehay) and Noam Hadad from Aleph Research came out with a theory that critical vulnerabilities using this mode that gives the hacker full access to your smartphone. However, this method requires physical access to the device but still, it is dangerous and cannot be patched. You can check out the list of devices that are affected by this exploit below:
- LG G4
- Nokia 6 (d1c)
- Nokia 5
- Nexus 6 (shamu)
- Nexus 6P (angler)
- Moto G4 Plus
- OnePlus 5 (cheeseburger)
- OnePlus 3T
- OnePlus 3
- OnePlus 2
- OnePlus X
- OnePlus One
- ZTE Axon 7
- ZUK Z1
- ZUK Z2
- Xiaomi Note 5A (ugglite)
- Xiaomi Note 5 Prime (ugg)
- Xiaomi Note 4 (mido)
- Xiaomi Note 3 (jason)
- Xiaomi Note 2 (scorpion)
- Xiaomi Mix (lithium)
- Xiaomi Mix 2 (chiron)
- Xiaomi Mi 6 (sagit)
- Xiaomi Mi 5s (capricorn)
- Xiaomi Mi 5s Plus (natrium)
- Xiaomi Mi 5x (tiffany)
- Xiaomi Mi 5 (gemini)
- Xiaomi Mi 3 (cancro)
- Xiaomi Mi A1 (tissot)
- Xiaomi Mi Max2 (oxygen)
- Xiaomi Redmi Note 3 (kenzo)
- Xiaomi Redmi 5A (riva)
- Xiaomi Redmi 4A (rosy)
Boot Sequence of Qualcomm Android Phone – Explained
SBL (Software Bootloader) is which is checked for authenticity before it is loaded to the memory chip imem. For naive, imem is a fast-on-chip that is used for debugging and DMA (direct memory access) and is exclusive to Qualcomm chipsets. Besides, in some device, XBL (extensive bootloader) is found in which the process of booting is the same. The SBL or XBL then launches the ABOOT (Android Bootloader) after which Fastboot is implemented. The SBL or XBL (in some occasions) check for the authenticity of signed or unsigned ABOOT.
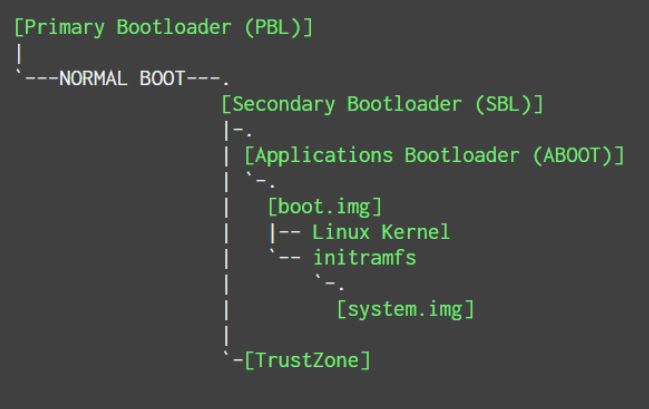
Once authenticated, ABOOT then checks /boot and /recovery for authenticity before launching the Linux kernel. Then some system operations are performed, and then code execution is transferred over to the kernel. Matter of fact, when we unlock the bootloader of a device, we are disabling this authenticity checking feature of ABOOT.
How to Gain Access?
Now, once you have some information about the boot sequence of a Qualcomm powered Android device, then let us head to the steps to gain access to EDL mode. Notably, Nokia device has short pins known as “test points” present on the mainboard. Moreover, devices having December 2017 security patch were easier to gain access to EDL by simply running “adb reboot edl” command.
Other smartphones use a “deep flash” cable which has certain pins for booting into the EDL mode. There are some old Xiaomi phones along with Nokia 5 and 6 that can make use of this cable.

Matter of fact, EDL mode can be utilized in several ways. One of the common ways is to unbrick the device by force flashing them. The worse scenario can be that the ABOOT will reject the software that is not officially signed. Besides, it is actually possible to gain full control of the OnePlus 3/3T devices. Basically there are two important commands that are required for the method to work:
fastboot oem disable_dm_verity
fastboot oem 4F500301/2
Below are the steps which allow you to gain access to the EDL on your OnePlus 3 and 3T.
- Firstly you need to boot into the EDL mode.
- Now you need to download a system image lower version than OxygenOS 4.0.2.
- Then, flash aboot.bin through Firehose.
- Keep in mind that aboot.bin implements Fastboot.
- You can now disable secure boot and unlock the bootloader without wiping the device simply by using the two Fastboot commands mentioned above.
Previously, OnePlus left two dangerous Fastboot commands vulnerable, one that unlocks the bootloader and the other one disables the secure boot. Hackers can take advantage of this situation and install the older version of the system image to gain access to the device just with the help of the above-mentioned commands. Firehouse works via Qualcomm’s Sahara protocol which when connected to a device, acts as an SBL over USB. This is used by many programmers to log into the EDL mode to gain full access to the device.
So, there you have it from my side in this post. I hope you guys liked it and were able to access EDL mode on OnePlus 3/3T. Let us know in the comments below if you come across any issues. Until the next post…Cheers!
Source: XDA