Malware is a common name for all kinds of malicious software, including computer viruses. The virus is different from the remnant of the malicious gang which usually infects the computer by entering it with the software installation, then replicated and in various ways spread further, both on your computer and other computers.
Long viruses were the most popular form of malicious software. But today they are no longer the most common. Adware – Software that throws the pile of ads – became popular thanks to suspicious web destinations and extras (extensions) for web browsers. Spyware, as his name says, spies and monitors your data and sends them to advertising companies. Ransomware, however, locks your computer and seeks ransom to re-enable you to access.
How does iOS protect your data?
Apple’s operating system has some embedded features designed to protect against malicious software.
Apple very strictly monitors the apps on the offer in its app store and does not allow anyone else installation for IOS applications. Although these applications are millions, theoretically each of them is viewed manually, and those in which malicious computer code received a refusal. This system is not perfect, but it is effective in removing the most potentially dangerous applications.
Each operating system, so also iOS, is important to regularly upgrade and refresh if you want to protect yourself from malware. Unlike android, whose users on software patches sometimes have to wait for months, IOS users get them immediately if the NIH’s device supports the edition for which they are intended. Therefore, the owners of the iPhone are more protected than older security failures.
That the iOS is safer does not mean it is completely protected. So far, there are more cases of malicious software for Apple devices. Your iPhone can have several problems that may seem like they are the result of viruses and malicious software, but in fact, have nothing to do with them.
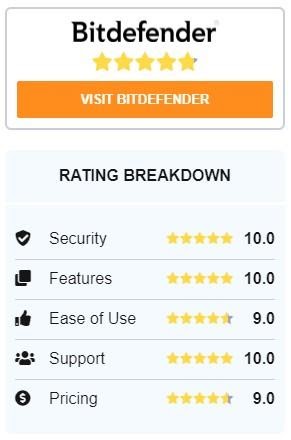
AntiVirus Protect – BitDefender as a safe residence
To make you feel comfortable and you do not get into security and protection problems, you need to use AntiVirus. BitDefender is one of the options that can help you. BitDefender grows day by day and steps with all the leading antivirus programs. To protect all your data and devices as well as the identity of all types of attacks. Slow you at all levels of e-mail the threat of attack on online banking systems. Whether you understand or not an antivirus, choose the one that is the best choice for you who will be most of the help.
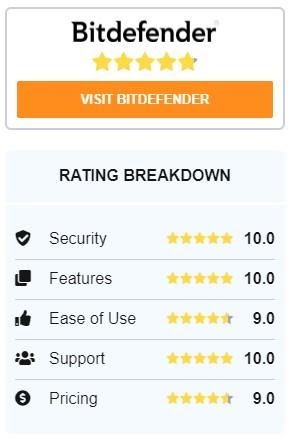
BitDefender detects, eliminates all types of attacks on devices. Provides protection even from the latest internet threats, within just a few seconds. BitDefender always offers optimal resistance, protection and you will never be in danger of new types of attack.
Think every time the Internet should leave the data
Before registration on the social network, we need to read the privacy settings. The problem occurs in cases where personal data is left, exchanged, collected, or wider further. All of the above may endanger the privacy of data. Therefore, when appropriate, we can be used by a pseudonym that does not reveal our personal information. Privacy can be linked to anonymity because anonymity is used as an instrument to achieve freedom or protect the privacy of a person.
We study the safety and privacy settings. We maximize the unwanted spread of our private information. Let’s respect privacy – both their own, as well as other users. The internet behavior is a user’s mirror. Our behavior affects the overall quality of the social network. If possible, include double-function authentication – additional login through the code to the device optionally – mostly our mobile device.
The internet is a place with lots of interesting information, but we all use it to search or communicate, often not thinking about where we leave our information like an e-mail address.
This is one of the reasons why we, before or after, are the target of those who want to earn on us or want us to use them.
If we get an offer that we will get something free, we need to consider whether it is valuable to leave personal data. Namely, the ancient wisdom says, “There is no such thing as a free lunch”. In other words, if something sounds too good to be true – probably not true!
Internet fraud can also occur through applications for communication such as Viber, WhatsApp, or others, where we get a message with the link and text that informs us that we have won something or just to visit the link to download the award, video, or other content.
Let’s be careful when there are situations around the media – whether it is celebrities, terrorist attacks, or humanitarian actions – criminals often use such situations for sending an electronic mail where we will try to persuade us to open a specific page or take off a file. In such situations, it is good to keep the web pages that we otherwise visit. News on them will be most likely proven and safer than elsewhere. Let’s not sit on the floor!
Nothing is free!
Most online services/services/platforms that are free for users are financed either through advertising or selling data of their users to advertisers. For example, many services including social networks rely on various elements to achieve advertising revenue. Among them is the maximization of user participation (sharing, commenting, posting, interaction, linkage, etc.) because they will enable them to sell more detailed information about their user’s advertisers and therefore increase the effectiveness of their advertising campaigns, which will target very specific users based on large the amount of data and information generated. You’ve probably noticed that when you click on a product, similar products are beginning to appear more frequently on your profile.
This also means that these services have an interest in keeping their profiles open (instead of locking your content completely, which would mean that your posts/activities will be visible to the limited audience) and keep as much as possible data on users ( Distracting them from “clean” their accounts regularly or delete a huge amount of past involvement and posts). See other people’s profiles – what you can read about them, they can read about you. Even when you publish your information or personal photos, you will have very little control over their use.